Strategy and transformation
Cyber assurance/attestation
Your challenges
- Is the business resilient to a cyber attack?
- Which threats should you be the most concerned about?
- Are there gaps in your cybersecurity capabilities?
- Do you have the right controls in place to detect key risks?
- Are we investing in the right areas?
What does it include
- Readiness assessment of your Cybersecurity Risk Management Program;
- Remediation assistance;
- Support in the report preparation and writing;
- Cybersecurity controls testing.
Key benefits
- Enhance brand and reputation;
- Provide transparency;
- Assess program effectiveness;
- Reduce communication and compliance burdens;
- Allow flexibility in reporting.


Cybersecurity transformation
Your challenges
- Do you want to undertake a comprehensive security assessment of your organisation?
- Do you want to identify technical and organisational weaknesses?
- Do you want to define an information security strategy aligned with your business objectives?
- Do you want to achieve a security posture aligned to your security risks and objectives?
What does it include
- Full assessment of your Cybersecurity maturity against PwC’s Cybersecurity framework;
- Support in the definition of a security strategy to reach a security maturity level aligned to your expectations;
- Roadmap to achieve this strategy, with detailed project sheets.
Key benefits
- Cybersecurity strategy and objectives defined, aligned with business objectives and security initiatives; identified, prioritised, planned and explained to achieve these objectives.
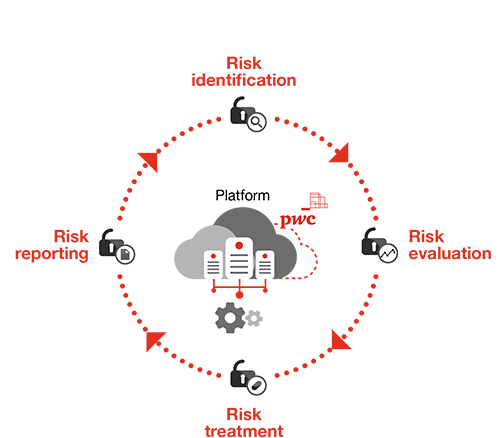
Information Security Risk Management
Your challenges
- Do you have a clear understanding of the risks impacting your data?
- Do you regularly monitor risks to ensure your protective measures remain appropriate and adapted to the threats you face?
- Are you aware of new risks arising from changes to your environment or external threats?
- Are your risk management activities compliant with the latest regulations (e.g. GDPR, CSSF, etc.)?
What does it include
- Outsourced risk management service that includes risk identification, assessment and reporting, run by our information security experts;
- Risk assessments tailored to your context and information systems;
- Assistance in developing risk treatment plans;
- Access to a web-based risk management tool (MONARC), which includes a central risk register.
Key benefits
- Timely access to threat intelligence feeds;
- Risk management informed by technical expertise;
- Standardised approach to risk management across the organisation.

Information Security Management System assessment & implementation
Your challenges
- Do you want to have a detailed analysis of the gaps between your current security practices and best practices (ISO27001, ISO27002)?
- Do you want to become compliant or certified with an internationally recognised security standard by implementing n Information Security Management System (ISMS)?
What does it include
An in-depth transformation process in three key phases:
- Gap analysis of the current situation;
- Implementation of the ISMS based on the tailored recommendations provided in the first phase;
- Preparation for the certification, white audit and support to prepare documents and evidence for the auditors.
Each phase can be selected individually depending on your needs.
Key benefits
- Detailed list of gaps and recommendations to achieve best practices;
- Support for the development of security documentation and governance required for an ISMS;
- Support for the deployment of security controls and procedures.
Network and Information Systems (NIS) Directive 2
Your challenges
- Are you aware that NIS2 has expanded scope of the previous Directive?
- Are you considering security measures to address the new obligations of the NIS2 Directive?
- Is your management aware of its new responsibilities and has programmed trainings to improve its cybersecurity skills?
What does it include
"Essential" and "important" entities, according to the new classification of service providers in scope, are obliged to:
- Adjust their incident reporting process according to the new reporting obligations
- Entitle members of the management body to approve and supervise cybersecurity risk management measures, who can be held liable for any breach
- Conduct a comprehensive risk assessment and implement cybersecurity measures to address vulnerabilities, threats and to mitigate risks
Key benefits
- Understand whether you fall under the NIS2 Directive
- Development and implementation of a roadmap to enhance compliance with the NIS2 Directive requirements
- Empower your Top Management with extensive knowledge and skills to guide the organisation's cyber strategy

SWIFT Customer Security Program
Your challenges
- Are you able to demonstrate compliance with the SWIFT Customer Security Programme (CSP)?
- Have you planned to attest your level of compliance against SWIFT CSP?
- Are you aware that SWIFT customers are required to support their attestation with an independent assessment against the CSP controls?
What does it include
- Compare what you have in place against the SWIFT framework, identify the discrepancies and the suitable corrective actions;
- Provide an independent assessment against CSP as requested by SWIFT;
Key benefits
- Understand your level of compliance against SWIFT CSP and align your strategy accordingly;
- Develop a roadmap to improve your SWIFT infrastructure maturity;
- Obtain an independent assessment by end of the calendar year as mandated by SWIFT.
Threat Intelligence
Your challenges
Do you have the intelligence needed to inform your cyber security operations and strategy?
Have you been the victim of a data leak?
Have you been targeted by an advanced cyberattack?
Is there a critical vulnerability affecting components of your infrastructure?
What does it include?
Threat Intelligence Landscape
Breach Notification
Typosquatting Domain Monitoring
Critical Vulnerability & Exploit Watch
Key benefits
We help you make informed risk-based decisions through a strategic outlook on the threat landscape for specific sectors, geographies and markets.
We alert you the moment a data breach is detected, allowing you to quickly make effective and educated decisions.
We alert you when a typosquatting attempt is detected, allowing you to take the required measures to mitigate the social engineering attempts.
We alert you the moment we identify a new critical vulnerability that may affect perimeter components.